First Party Data Strategy for Accurate Marketing Attribution Under Safari ITP
Marketing measurement once depended on browser-controlled identifiers. Cookies connected ad clicks, sessions, and conversions over time. That foundation is no longer reliable.
Browser privacy controls now decide how long data survives. Cookies expire early. Returning users lose identity. Attribution windows collapse without notice.
This change affects a large share of real traffic. Safari accounts for over 51.12% of mobile browser usage in the United States, meaning half of mobile conversions are exposed to aggressive tracking restrictions by default.
A first-party data strategy shifts ownership away from the browser. Events are collected, validated, and transmitted through the business-controlled infrastructure. Identity does not depend on short-lived client-side storage.
Without this shift, teams analyze partial journeys. Campaign performance looks worse than it is. Optimization decisions are based on missing signals.
To understand why this happens and how to fix it, you first need to understand how Safari changed the rules.
TL;DR
- Safari ITP limits first-party cookies set via JavaScript to seven days, or 24 hours for traffic from classified ad sources, breaking attribution for longer buying cycles.
- Identity loss causes returning users to be counted as new, leading to misattributed conversions and distorted ROAS, CPA, and audience performance.
- Common browser-based workarounds fail because Safari controls client-side storage and actively removes tracking signals.
- A first-party data strategy moves event collection and identity management to server-controlled infrastructure, outside browser restrictions.
- Server-side tracking with persistent first-party identity restores accurate attribution and prepares marketing measurement for future privacy changes.
Safari ITP and the Breakdown of Browser-Based Tracking
Safari limits tracking by design. These limits are enforced through Intelligent Tracking Prevention (ITP), a system built directly into Apple’s WebKit browser engine.
ITP was introduced to stop cross-site tracking. At first, it focused on third-party cookies. When tracking vendors shifted to first-party cookies set through JavaScript, Apple extended the restrictions.
Today, Safari does not treat browser-set identifiers as reliable storage. Cookies created by tracking scripts are automatically shortened or removed. The process happens without errors, warnings, or visible failures.
From a marketing perspective, this creates a hidden problem. Events still fire, but identity does not persist. Returning users are gradually disconnected from earlier interactions.
This is not a configuration issue. It is a structural limitation of Safari’s browser-based tracking.
That limitation becomes more severe as ITP evolves.
The Technical Evolution of ITP and Identity Restrictions
Apple did not introduce ITP all at once. The restrictions expanded in stages, each closing a path marketers relied on to preserve identity.
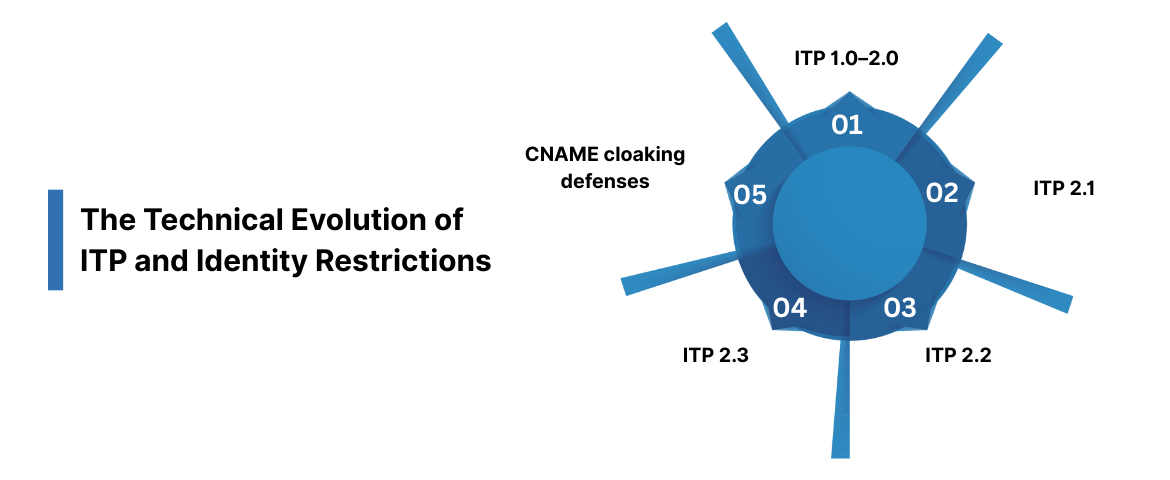
ITP 1.0–2.0: Blocking third-party cookies
Early versions focused on third-party cookies. If a tracking cookie was set by a domain different from the site being visited, Safari blocked it. This removed classic cross-site tracking but left first-party cookies untouched.
ITP 2.1: Limiting first-party JavaScript cookies
In 2019, Apple shifted its approach. Cookies created via JavaScript using document.cookie were capped at seven days. This applied even when the cookie was set on the brand’s own domain.
At this point, identity persistence began to break for longer buying cycles.
ITP 2.2: Link decoration and the 24-hour window
Apple then targeted link decoration. If a user arrived via a URL containing tracking parameters from a “classified” domain, such as Facebook or Google, Safari reduced cookie lifetime to 24 hours.
This change directly affected paid acquisition.
ITP 2.3: Extending limits beyond cookies
Trackers attempted to bypass cookie limits using localStorage. Apple responded by applying the same expiration rules to all client-side storage. Identity data stored in the browser was treated the same way.
CNAME cloaking defenses
Some vendors used CNAME cloaking to disguise third-party trackers as first-party subdomains. Safari now detects this behavior and automatically applies the same restrictions.
Each update followed the same pattern. When tracking moved within the browser, Safari followed and restricted it.
This evolution explains why identity loss is unavoidable when tracking depends on client-side storage.
How the Seven-Day Window Breaks Attribution in Practice
The most disruptive changes arrived with ITP 2.1 and 2.2. These updates targeted first-party cookies created through JavaScript. If a tracking script sets a cookie in the browser, Safari now limits its lifespan to seven days.
In some cases, the restriction is even shorter. When a user arrives from a classified tracker, such as a Facebook or Instagram ad, Safari reduces the cookie window to 24 hours. This applies when the visit is made via a decorated link that includes tracking parameters.
The reasoning is intentional. Apple treats long-term tracking without explicit consent as a privacy risk. By shortening cookie lifetimes, Safari automatically resets user identity. Once the window closes, past interactions are no longer connected.
The 8-Day Identity Breakdown
This impact becomes clear in a common buying scenario.
Day 1: The interaction
A user scrolls Instagram on an iPhone and clicks a paid ad for a $200 product. The ad link includes tracking parameters. When the site loads, analytics and ad pixels fire, creating a first-party cookie to identify the user.
Safari detects the decorated link and flags the cookie. A 24-hour expiration timer is applied.
Days 2–7: Consideration
The user does not purchase immediately. They consider the product and take no further action during the week.
Day 8: Conversion
The user returns by typing the site URL directly or reopening a saved tab. They complete the purchase. At this point, the cookie no longer exists. Safari has already removed it.
The result
Analytics registers a new user. The traffic source is labeled Direct. The Instagram ad that started the journey receives no attribution. Reported ROAS declines, and CPA appears inflated.
What makes this dangerous is the decision that follows. A marketer reviewing the data may pause or reduce the campaign’s spend, assuming it underperformed. In reality, the campaign drove the sales. The identity connection was simply erased.
This is how Safari ITP undermines attribution. Events still occur, but identity does not persist long enough to link them.
Why Safari ITP Skews Marketing Performance Data
When Safari removes identity, the problem does not appear as a tracking error. It shows up as bad decisions driven by believable data.
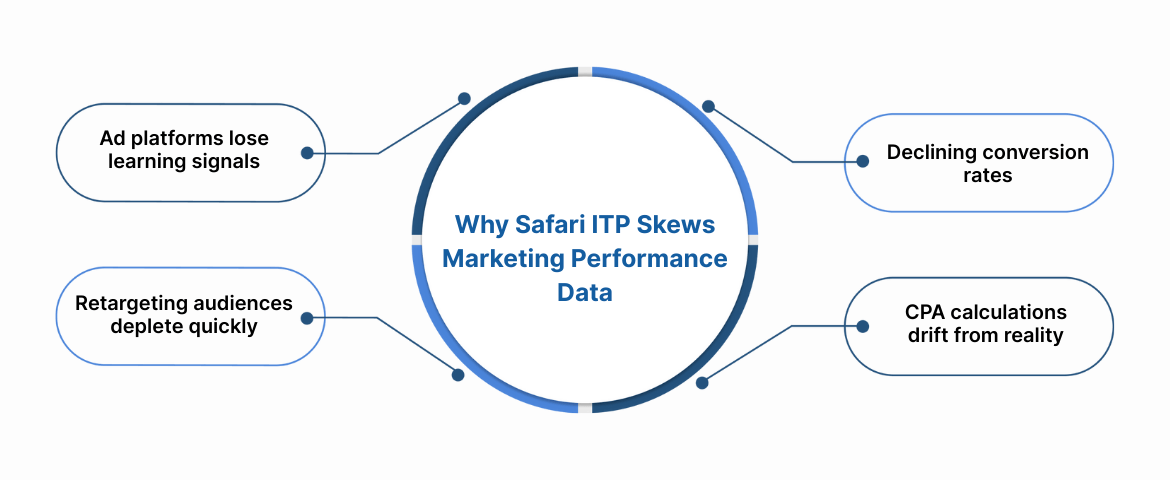
Ad platforms lose learning signals
Ad delivery systems optimize based on conversion feedback. When a purchase occurs after Safari deletes the identifier, that conversion does not feed back into the platform. Over time, the algorithm begins to optimize for weaker signals because the strongest ones are missing.
Performance does not drop immediately. It degrades quietly.
Conversion rates decline without traffic changes
Returning users who convert after seven days are counted as new visitors. Traffic increases on paper. Conversions do not. Conversion rate drops, even though user behavior did not change.
Teams often respond by redesigning landing pages or adjusting offers. The issue is not the page. It is identity loss.
Retargeting audiences empty faster than expected
Add-to-cart and product-view audiences depend on recognition. When Safari expires identifiers in seven days, users leave these audiences before they are ready to buy. Retargeting spend shifts toward colder users with lower intent.
The funnel still exists. The audience visibility does not.
CPA calculations drift from reality
Cost per acquisition is calculated using tracked conversions. If Safari hides even 25–30% of those conversions, CPA appears significantly higher. Budgets are reduced or reallocated based on incomplete attribution.
This is how profitable campaigns get paused. Not because they failed, but because Safari removed the evidence that they worked.
Safari ITP does not break dashboards. It breaks the assumptions teams rely on to interpret them.
The Browser-Level Mechanics Behind Signal Loss
Safari enforces tracking restrictions at the browser level, not through tag rules or platform settings. Once a domain is classified as a tracker, storage limits are automatically applied to the user’s device.
This classification happens locally. Safari analyzes how domains behave across sites and applies restrictions without relying on external lists or configurations. Marketers have no visibility into when or why a domain is flagged.
Once restricted, Safari limits or removes key forms of storage:
- Cookies created via JavaScript are capped at seven days
- Ad-click cookies from classified trackers are capped at 24 hours
- LocalStorage and similar storage are purged after seven days of inactivity
- Referrer data is reduced to the root domain, removing campaign context
The result is predictable. Identity stored in the browser decays quickly, even when users return naturally.
This is why client-side fixes fail. No amount of tag tuning can extend cookie lifetimes or preserve identity once Safari enforces its limits. The browser owns the storage, not the tracking script.
To illustrate the difference, the behavior looks like this:
- Standard browsers: identifiers persist for months or years
- Safari with ITP: identifiers reset every seven days, or sooner
From a measurement perspective, this creates fragmented journeys. From a systems perspective, it means browser storage can no longer be trusted as the foundation for identity.
This is the point at which teams must rethink where identity and event data should reside.
Why Browser-Level Fixes Fail Against Safari ITP
Most tracking workarounds fail because they try to outsmart the browser rather than change where identity lives. Safari controls the client. Anything stored or inferred there remains temporary.
Fingerprinting breaks at the signal level
Device-based identifiers rely on attributes such as screen size, OS version, and hardware details. Safari now reduces the precision of these signals and randomizes values over time. The same device no longer looks consistent across sessions, making fingerprints unstable and unusable for attribution.
Bounce tracking collapses immediately
Redirect-based tracking depends on capturing identity during a brief handoff between domains. Safari detects these redirect patterns and clears associated storage as soon as the flow completes. Any identifier created during the bounce is discarded before it can be reused.
URL-based identity does not persist
Passing IDs through URLs creates fragile dependencies. Parameters are stripped, links break, and identifiers leak into logs and referrers. Safari actively limits the effectiveness of this approach by removing known tracking parameters when detected.
CNAME cloaking no longer extends identity
Masking third-party trackers behind first-party subdomains once detection is delayed. Safari now inspects CNAME mappings and applies the same storage restrictions when a subdomain resolves to a known tracking endpoint.
Each method fails for the same reason. Identity is still created and stored in the browser. Safari enforces expiration regardless of how that identity was generated.
This is why a first-party data strategy cannot rely on client-side persistence. To maintain continuity, identity must be issued and managed outside the browser.
What a First-Party Data Strategy Actually Requires
A first-party data strategy changes where identity lives.
As long as identity is created and stored in the browser, it will expire on the browser’s terms. Safari has made that clear. A first-party strategy moves identity and event control to the business’s own infrastructure. That requires three things.
- Server-owned event collection: Events must be received and validated by your own server before being sent to analytics or ad platforms. Browser scripts become input sources, not the system of record.
- Identity issued outside JavaScript: Identifiers cannot rely on JavaScript-accessible cookies or browser storage. They must be set and managed server-side, with their lifespan and access rules not dictated by Safari.
- Consent is enforced before data leaves your stack: User consent determines which events and identifiers are processed during ingestion. Filtering data after it reaches third-party platforms is already too late.
When these conditions are met, attribution windows reflect real buying behavior. Returning users stay connected to earlier interactions. Measurement remains stable even as browser rules change.
That is what separates a first-party data strategy from short-term tracking fixes.
A Server-First Approach to First-Party Data
Browser-level restrictions cannot be fixed with more browser code. As long as identity is created through JavaScript and stored client-side, Safari will continue to shorten or delete it.
Solving this requires shifting where tracking happens, not how scripts behave.
This is where Ingest Labs enables a structural change by moving data collection and identity management away from the browser and into server-controlled infrastructure.
Ingest IQ: Server-Side Event Collection
Ingest IQ changes the direction of data flow.
Instead of sending events directly from the user’s browser to platforms such as Meta or Google, events are first sent to a business-controlled server endpoint. From there, data is forwarded to ad platforms, analytics tools, or internal systems.
This server-to-server flow removes the browser as the system of record.
Because events originate from your domain and are processed server-side, Safari’s storage limits no longer affect event delivery. Purchases, page views, and conversions are captured consistently, even when browser identifiers expire.
The result is cleaner event data and attribution that reflects actual user behavior rather than browser constraints.
Ingest ID: Extending Identity Beyond Cookie Limits
Capturing events is only part of the equation. Attribution still depends on identity continuity.
Ingest ID provides a persistent, first-party identifier that does not rely on JavaScript-accessible storage. When a user visits, an identifier is issued server-side and stored using an HttpOnly cookie.
Because this cookie cannot be accessed by JavaScript, Safari treats it as site data rather than tracking data. This allows identity to persist for 180 to 365 days rather than expiring after a few days.
This approach maintains continuity across longer buying cycles without relying on fragile browser storage.
How This Changes Measurement
Capability
Standard Pixel Tracking
Ingest IQ + Ingest ID
Cookie lifespan in Safari
1–7 days
180–365 days
Event capture
Partial
Nearly complete
Attribution window
Breaks after 7 days
Full customer journey
Ad spend efficiency
Misallocated due to blind spots
Improved with clean data
Setting Up a Server-Side First-Party Data Foundation
Moving to server-side tracking does not require rebuilding your entire stack.
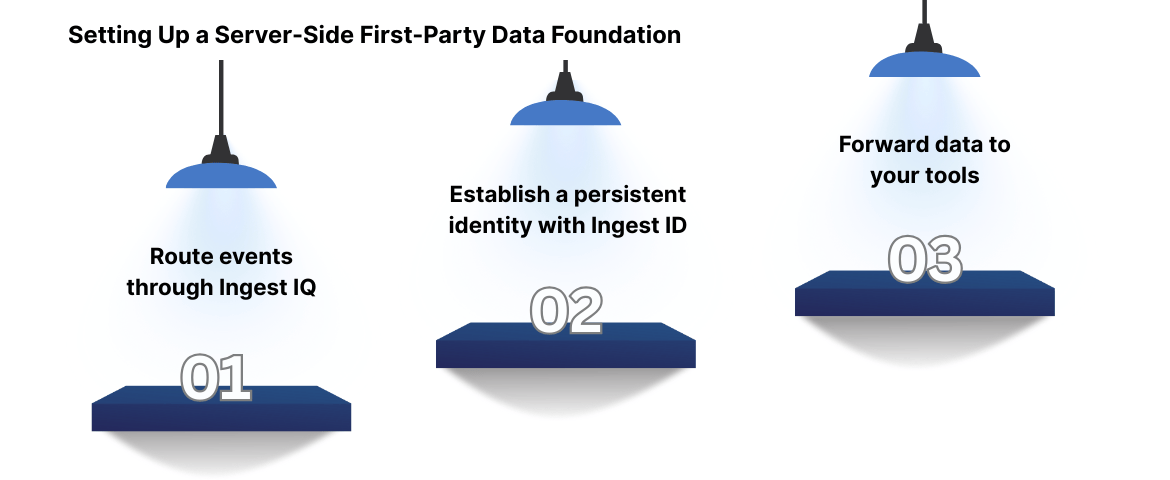
Step 1: Route events through Ingest IQ
A single script acts as a gateway, sending events to your server endpoint instead of directly to third-party platforms.
Step 2: Establish a persistent identity with Ingest ID
User sessions and interactions are linked by a unified identifier, ensuring continuity across visits and devices.
Step 3: Forward data to your tools
Events can be sent to destinations such as Meta Conversions API, Google Analytics 4, or internal systems, without duplicating logic in the browser.
Once this foundation is in place, browser updates no longer dictate what data you see. Measurement reflects reality, not storage limits.
The Business Economics of Clean First-Party Data
Data loss directly impacts how marketing budgets are spent and scaled.
When attribution is incomplete, spend is optimized against partial signals. That distortion compounds quickly.
Consider a common scenario:
- Monthly ad spend: $10,000
- Conversions hidden by Safari ITP: ~30%
- Budget optimized on incomplete data: $3,000 per month
- Annual impact: $36,000 allocated without accurate attribution
This gap affects more than reporting. It changes behavior.
- High-performing campaigns appear underwhelming and get paused.
- Bids are lowered because the return appears weaker than it is.
- Growth stalls as teams become cautious based on misleading metrics.
Clean first-party data reverses this.
With full visibility into delayed and repeat conversions:
- True conversion value becomes measurable.
- Bidding decisions reflect actual performance.
- Campaigns scale based on confidence, not assumptions.
Real-World Impact
Teams that restore attribution clarity see fast results. In one case, improved first-party signal capture led to a 22% increase in tracked conversions within 30 days. With stronger feedback, Meta’s delivery algorithm stabilized, CPA declined, and scaling became predictable again. The advantage is not spending less. It is spent with certainty.
The Privacy Shift Makes Server-Side Ownership Non-Negotiable
Safari exposed the weakness of browser-based tracking. Chrome is now formalizing it through the Privacy Sandbox. While the implementations differ, the outcome is consistent. Tracking that depends on the browser is becoming less reliable by design.
Browsers are asserting control on the client side. Cookie lifetimes are shortened. Storage is restricted. Signals are filtered before they ever reach analytics or ad platforms. These changes are permanent.
Accuracy depends on where the data is processed. When events and identifiers live only in the browser, browsers decide how long they survive. When data is collected and governed on the server side, those limits no longer apply.
Server-side ownership changes the fundamentals:
- Speed: Fewer client-side scripts reduce execution overhead and improve page performance.
- Control: Data is shared intentionally, not implicitly, with third-party platforms.
- Accuracy: Events persist beyond browser-imposed limits, such as ITP and ad blockers.
This is why a first-party data strategy cannot rely on client-side persistence. It requires infrastructure that the business controls end-to-end.
Platforms like Ingest Labs enable this shift by supporting server-controlled event collection and identity, allowing teams to operate independently of browser policy changes.
As privacy enforcement expands, ownership, not optimization, becomes the deciding factor.
Conclusion
Safari ITP exposed a core weakness in modern marketing stacks: identity that lives in the browser cannot be trusted over time. Cookies expire early, attribution resets, and performance data slowly drifts away from reality.
A first-party data strategy fixes this at the foundation. When events and identity are controlled server-side, buying cycles longer than a few days remain measurable. Conversion signals stay intact. Budget decisions are based on complete journeys, not browser-imposed limits.
This is not about adapting to Safari alone. Chrome, regulation, and platform policies are moving in the same direction. Data ownership determines accuracy going forward.
Learn how to strengthen your first-party data foundation with Ingest Labs.