Understanding SOC 2 Type II Compliance and Certification
With the increasing frequency of cyberattacks and data breaches, businesses must prove they are taking adequate measures to protect sensitive data. One way to demonstrate your commitment to data security is by obtaining SOC 2 Type II certification. This certification assures customers that your organization follows strict security protocols, ensuring their data is safe and protected.
In this blog, we will break down SOC 2 Type II certification, explain its importance, and guide you through the process of obtaining it.
Before we look further, let’s define what SOC 2 Type II certification really means.
What is SOC 2 Type II Certification?
SOC 2 (System and Organization Controls 2) is a framework developed by the American Institute of Certified Public Accountants (AICPA) to assess and ensure the security, availability, processing integrity, confidentiality, and privacy of data handled by service organizations. SOC 2 is primarily designed for technology and cloud computing companies that manage client data, especially those in SaaS (Software as a Service) and other service-based industries.
SOC 2 certification is divided into two types:
- SOC 2 Type I evaluates the design and implementation of controls at a specific point in time.
- SOC 2 Type II evaluates the effectiveness of these controls over a period of time, typically 6 to 12 months.
Achieving SOC 2 Type II certification means that your organization has not only designed the necessary controls to safeguard data but has also maintained those controls consistently over time. This certification is an essential step for any business that handles sensitive customer data, as it demonstrates that your security practices are both robust and reliable.
Related Read: How Ethical Data Collection Builds Trust and Fuels Business Growth
With a clear definition in mind, let’s explore why this certification is so crucial for your business.
Why is SOC 2 Type II Certification Important?
SOC 2 Type II certification is important for several reasons, especially in today’s highly competitive and regulated business environment. It not only helps businesses prove their commitment to data security but also builds trust with customers, partners, and stakeholders. Here are some key reasons why SOC 2 Type II certification is crucial:
- Compliance:
SOC 2 Type II certification helps ensure compliance with various regulations such as GDPR and CCPA. It also reduces the risk of penalties and legal issues related to data security violations. - Competitive Advantage:
Having SOC 2 Type II certification can give your company a competitive edge in the marketplace. Clients are more likely to trust businesses that have third-party verification of their security practices, which can lead to increased business opportunities. - Builds Trust with Clients:
As more businesses move to the cloud, clients are increasingly concerned about the security of their data. SOC 2 Type II certification provides a third-party validation that your organization has the proper security controls in place to protect client information. This helps build trust and confidence in your service offerings. - Ensures Data Security Compliance:
Many industries are subject to strict regulatory requirements regarding data security, privacy, and confidentiality. Achieving SOC 2 Type II certification demonstrates your organization’s commitment to compliance with these regulations. It also helps avoid penalties and legal complications that could arise from non-compliance. - Mitigates Risk:
Obtaining SOC 2 Type II certification forces your organization to assess and improve its security practices regularly. This proactive approach to risk management helps identify vulnerabilities and reduce the likelihood of security breaches, ultimately protecting your company and its clients. - Improves Internal Controls and Processes:
The process of achieving SOC 2 Type II certification often involves reviewing and improving internal controls. This can lead to better security practices and operational efficiencies that benefit the business overall.
Learn more about Understanding the General Data Protection Regulation (GDPR)
Next, we’ll break down the five key trust service criteria that form the backbone of SOC 2.
The 5 Trust Service Criteria of SOC 2
SOC 2 Type II certification is based on five key Trust Service Criteria (TSC), each of which focuses on a crucial aspect of data security, privacy, and integrity. These criteria are designed to ensure that organizations handle sensitive data responsibly and protect it from risks, breaches, and unauthorized access. Achieving SOC 2 Type II certification means your organization has demonstrated that it meets these standards over time. Let's explore these criteria in more detail:
- Security:
This criterion ensures that the system is protected against unauthorized access, both physical and logical. This includes measures such as firewalls, encryption, intrusion detection systems, and employee access controls to prevent security breaches. - Availability:
This criterion ensures that the system is available for operation and use as agreed or as required by the customer. It involves ensuring uptime, system performance, and the ability to recover quickly from disruptions. - Processing Integrity:
This focuses on ensuring that the system processes data accurately, timely, and in accordance with business objectives. It aims to ensure that data is processed correctly without errors, delays, or omissions. - Confidentiality:
Confidentiality refers to the protection of sensitive information, such as client data, from unauthorized access or disclosure. Organizations must take steps to ensure that data is stored securely and only accessible by authorized individuals. - Privacy:
This criterion focuses on the handling of personal information in a manner that complies with privacy laws and regulations. It ensures that personal data is collected, processed, stored, and disclosed in accordance with privacy policies and agreements.
These five criteria form the foundation of SOC 2 Type II certification and help ensure that companies are protecting their customers’ sensitive information across all stages of data processing and storage.
Now that we understand the criteria, let’s walk through the step-by-step process of achieving SOC 2 Type II certification.
The SOC 2 Type II Certification Process
Achieving SOC 2 Type II certification involves several key steps, and it typically takes 6 to 12 months to complete the process. Here is an overview of the steps involved:
- Preparation and Gap Analysis:
The first step is to assess your organization’s current security and privacy controls. This often involves performing a gap analysis to identify areas where your practices do not align with SOC 2 requirements. This step is critical to ensuring that your organization is fully prepared for the audit. - Design and Implement Security Controls:
Once gaps have been identified, your organization needs to design and implement appropriate security controls. This might involve updating your data protection policies, implementing new access controls, or enhancing your network security measures. It’s important to ensure that your security controls align with the five trust service criteria of SOC 2. Server-Side Tagging can play a significant role in this phase by ensuring data is processed securely. - Audit by a Third-Party Firm:
After your organization has implemented the necessary security controls, you will undergo an audit conducted by an independent third-party firm. The auditors will evaluate your security practices and controls to ensure they are effective and meet SOC 2 requirements. - Documentation and Evidence Collection:
During the audit, your organization must provide documentation and evidence of its security practices, such as system configurations, user access logs, and other relevant records. The auditors will review these documents to assess whether your controls are working as intended.
Learn more about: How Cookieless Tracking Works and Its Impact on Data Collection - SOC 2 Report and Certification:
After the audit is complete, the third-party auditor will prepare a SOC 2 report. If your organization passes the audit, you will receive the SOC 2 Type II certification, confirming that your security practices meet the required standards.
Learn more about: How Ethical Data Collection Builds Trust and Fuels Business Growth
To support your certification journey, let’s see how Ingest Labs can help streamline the process.
How Ingest Labs Helps with SOC 2 Type II Certification
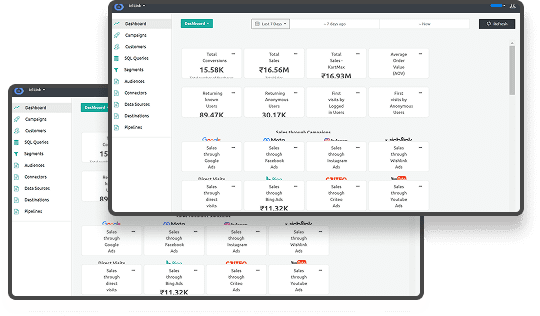
Ingest Labs provides a comprehensive suite of solutions that are SOC 2 Type II certified.
By implementing server-side tagging, Ingest Labs ensures that data collection is handled securely and efficiently, minimizing reliance on third-party cookies and reducing exposure to potential vulnerabilities. This approach not only streamlines your data processing but also ensures that you maintain compliance with stringent security protocols.
Ingest Labs offers real-time data streaming capabilities, which allow you to monitor your security controls continuously. This real-time insight is crucial for early detection of anomalies and ensures that any potential issues are addressed promptly.
Ingest Labs also supports seamless integration with over 100 marketing and analytics tools. This broad integration capability ensures that your entire ecosystem remains secure and compliant, aligning with privacy and security best practices as described in Understanding First-Party, Second-Party, and Third-Party Data: Strategies and Benefits.
By adopting Ingest Labs’ technology, you can simplify the process of achieving SOC 2 Type II certification, improve your operational efficiencies, and build a stronger security posture that reassures both regulators and clients alike.
Conclusion
SOC 2 Type II certification is a critical step for businesses that handle sensitive data and want to build trust with their clients. It demonstrates your commitment to data security and privacy by ensuring that your security controls are effective and consistent over time. The certification process can be challenging, but the benefits are well worth the effort, from enhancing client trust to improving overall data security and compliance.
Ingest Labs offers solutions that are SOC 2 Type II certified ensuring your entire marketing data collection, processing, storage and transmission are secure. Our robust data collection practices align with the highest security standards, facilitating compliance with regulations such as GDPR and CCPA. By leveraging Ingest Labs' services, you can enhance your organization's data security posture and build stronger client trust.